Chinese cyberspies breached dozens of telecom firms, govt agencies
Chinese cyberspies, tracked as UNC2814 by Google, have been sneaking into telecom and government networks worldwide since at least 2023, hitting 53 orgs in 4...
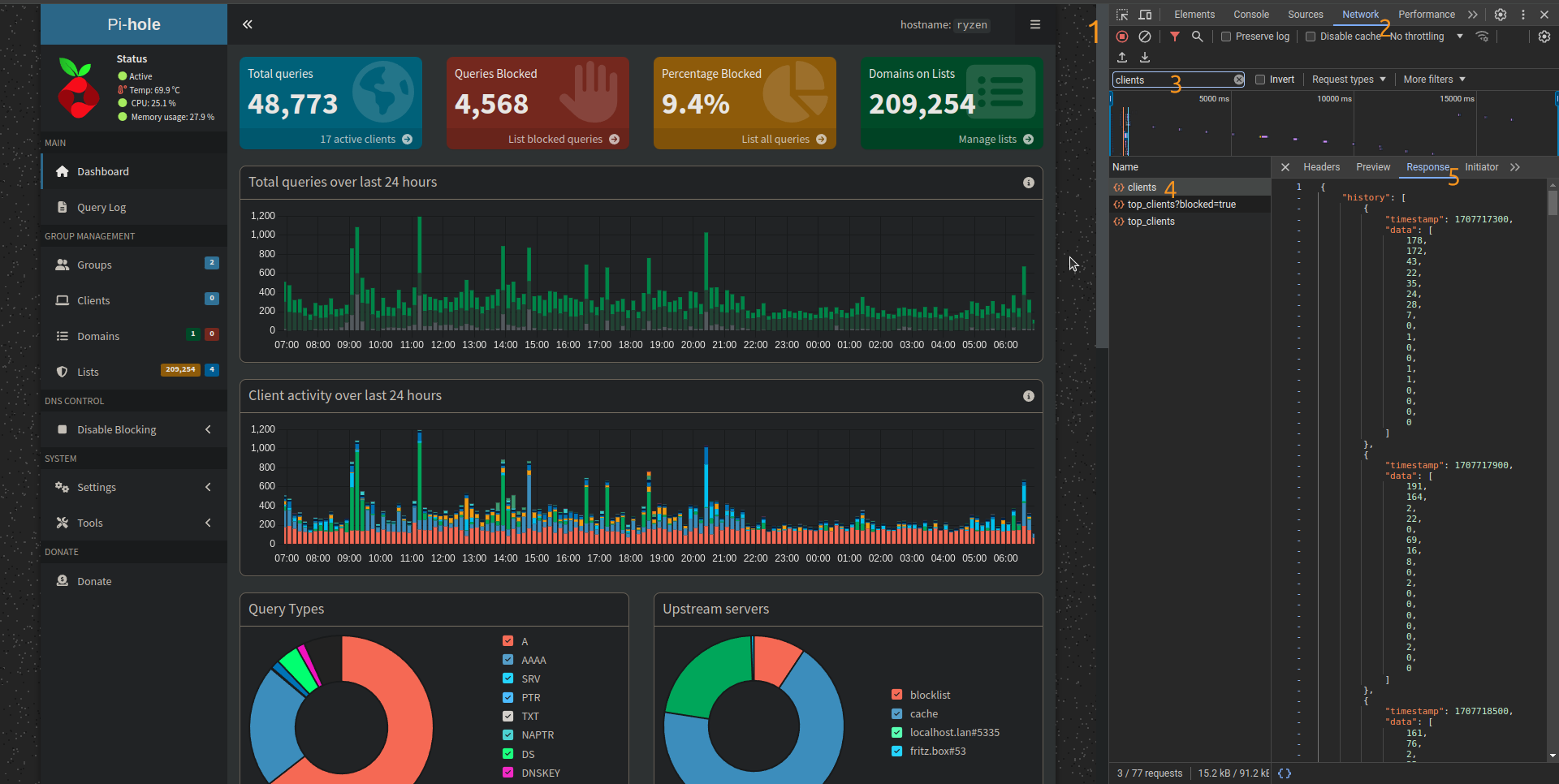
Are you looking for a reliable way to block annoying ads and improve your network security? Pi-hole, combined with Docker Compose, offers a flexible solution that works on a wide range of hardware. This guide will take you through the basic steps to set up Pi-hole using Docker Compose, making it easy to deploy on any system that supports Docker.
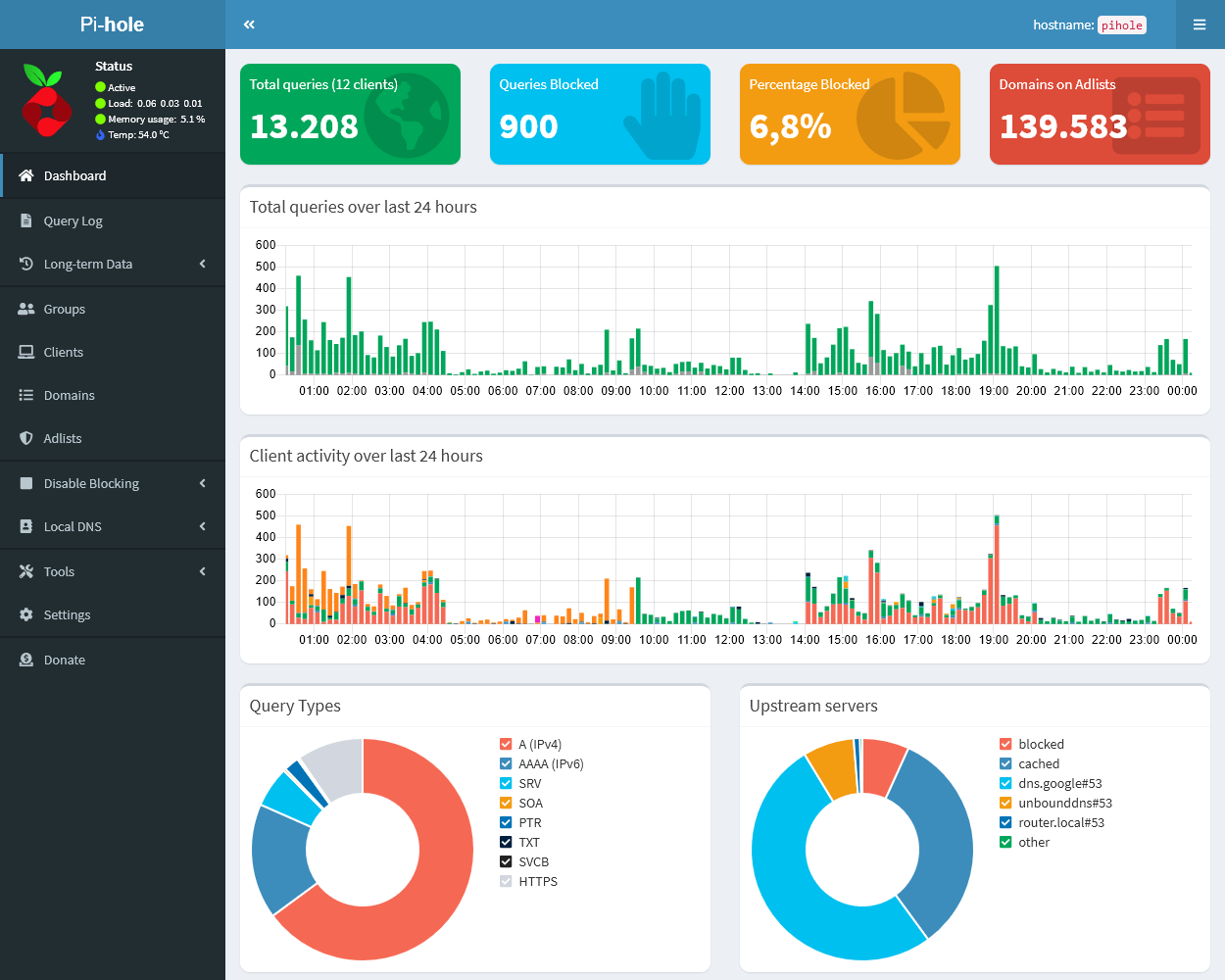
Pi-hole is a powerful network-wide ad blocker that prevents unwanted ads from reaching your devices. By blocking access to malicious domains, it also adds an extra layer of security to your network, making your browsing experience faster and safer.
Using Docker Compose to set up Pi-hole allows for easier management and deployment across different hardware platforms. Whether you’re running a Raspberry Pi or a high-performance server, Docker Compose simplifies the installation process, keeps your system organized, and makes future updates more manageable.

sudo apt-get update
sudo apt-get install docker.io docker-compose
mkdir pihole
cd pihole
docker-compose.yml file with the following content:
version: "3"
services:
pihole:
container_name: pihole
image: pihole/pihole:latest
environment:
TZ: 'America/New_York' # Set your timezone
WEBPASSWORD: 'yourpassword' # Set a password for the admin interface
volumes:
- './etc-pihole:/etc/pihole'
- './etc-dnsmasq.d:/etc/dnsmasq.d'
networks:
- pihole_network
ports:
- "53:53/tcp"
- "53:53/udp"
- "80:80"
- "443:443"
restart: unless-stopped
networks:
pihole_network:
sudo docker-compose up -d
The -d flag runs Pi-hole in detached mode, allowing it to continue running in the background.
http://<your-server-ip>/admin.docker-compose.yml file.Now that you have Pi-hole up and running, you’ve made a significant leap toward a more secure, ad-free network. But this is just the beginning! Check out the advanced configuration article
Stay tuned for more in-depth guides on how to enhance your network’s security!
Need Help?
If you need assistance with the setup or prefer a professional touch, Subvertec is here to help. Contact us today to secure your network and enjoy an ad-free browsing experience.
Chinese cyberspies, tracked as UNC2814 by Google, have been sneaking into telecom and government networks worldwide since at least 2023, hitting 53 orgs in 4...
Look, if you’re a tech-savvy SMB owner or MSP dealing with AI tools, you might be wondering the same thing as this Hacker News poster: have the big AI resear...
Cybersecurity researchers at Check Point have exposed a clever hack where bad actors exploit AI chatbots like Grok and Microsoft Copilot for under-the-radar ...
Skullcandy’s latest Method 540 ANC earbuds are basically a rehash of the popular Method 360 model, with the same design, drivers, and sound profile that made...
Figure Technology Solutions, a blockchain-based fintech player that’s all about lending and trading, just got hit by a sneaky social engineering attack from ...
VectorWare is shaking things up by making Rust’s async/await work directly on GPUs, letting developers ditch the manual concurrency mess and use familiar abs...
If you’re a small-business owner or MSP eyeing AI without breaking the bank, the Acer Aspire 14 AI Copilot+ PC is a steal at just $460—down from $830, dodgin...
Google just dropped an emergency patch for the first Chrome zero-day vulnerability of the year, CVE-2026-2441, which is already being exploited in the wild—t...
CISA’s just dropped the hammer, giving federal agencies a tight three-day window to patch a nasty remote code execution flaw in BeyondTrust’s Remote Support ...
Central Maine Healthcare just fessed up to a nasty data breach from last year, where hackers lurked in their systems for over two months between March and Ju...
Apple’s finally admitting defeat with its lackluster in-house AI for Siri and is partnering with Google for a multi-year deal, swapping in Google’s more robu...
Anthropic is rolling out its Claude AI platform to the healthcare sector with HIPAA-compliant Enterprise tools, following OpenAI’s playbook for ChatGPT, and ...
Democratic senators are calling out Apple and Google for turning a blind eye to X’s AI chatbot, Grok, which is essentially letting users generate creepy, non...
The Illinois Department of Human Services just fessed up to a major data blunder, where sensitive info like names, addresses, and case details for over 670,0...
Microsoft’s Copilot AI is facing scrutiny over prompt injection and sandbox bypasses that a security researcher claims are vulnerabilities, but the company d...
NordVPN is pushing back hard against claims of a server breach, insisting that hackers only snagged some harmless “dummy data” from a temporary third-party t...
Google’s rolling out a new image AI model, Nano Banana 2 Flash, as part of its speedy Gemini Flash lineup, promising to crank out visuals faster than the bee...
Investigations by TRM Labs have pinned a string of cryptocurrency heists on the 2022 LastPass breach, where hackers swiped encrypted vaults containing wallet...
The European Space Agency (ESA) has fessed up to a cyberattack on some of its external servers, which held unclassified data related to collaborative enginee...
With winter storms knocking out power left and right, Anker’s 521 PowerHouse portable battery is a smart, no-nonsense backup for tech-savvy small-business ow...
AI’s rise in education is a double-edged sword, potentially bridging the yawning inequality gap by offering affordable, always-on tutoring tools like custom ...
AI coding agents are basically supercharged LLMs that help automate coding tasks, but they’re handcuffed by context limits that cap how much code they can ju...
ZDNET’s 2025 Best of awards spotlight over 35 gadgets that aced our brutal real-world tests, from ultra-thin foldables to AI tools that actually deliver on p...
Google’s Gemini and OpenAI’s ChatGPT chatbots, despite their built-in guardrails, are being exploited by shady users to whip up deepfake images that strip fu...
Baker University’s recent data breach, stemming from a December 2024 intrusion, exposed sensitive info like Social Security numbers, financial details, and h...
Diving into the best home automation systems for 2025, it’s all about balancing tech smarts with your wallet—think startup costs for the basics like a $50-$2...
South Korea’s e-commerce giant Coupang just fumbled a massive data breach, exposing the personal info of 33
As OpenAI scrambles with its “code red” alert to outmaneuver Google—echoing the search giant’s own panic-fueled layoffs a few years back—it’s easy to see why...
The notorious Clop ransomware crew is at it again, zeroing in on exposed Gladinet CentreStack servers to pull off data theft and extortion schemes, exploitin...
If you’re a tech-savvy traveler eyeing a winter jaunt to Japan and tired of fumbling with airport SIMs or flaky WiFi, snag this exclusive deal: ByteSim is ho...
Look, if you’re an SMB or MSP diving into AI chatbots for customer service or internal tools, don’t kid yourself—these systems are basically digital elephant...
Docker’s rolling out free hardened images to bolster container security, making it easier for SMBs and MSPs to lock down their ecosystems without breaking th...
If you’re running a small business and rely on AI chatbots like ChatGPT or Gemini for quick insights, watch out—extensions such as Urban VPN Proxy and its sh...
Artie’s YC-backed CDC platform is streamlining real-time data replication from databases to warehouses with minimal fuss, making life easier for engineering ...
Netflix’s latest trailer for Stranger Things Season 5, Volume 2—dropping in just 10 days—gives fans a glimpse of episodes five through seven, building on the...
In 2025, phishing attacks got craftier than ever, with hackers ditching email for an omni-channel free-for-all, like sneaky LinkedIn DMs and rigged Google se...
When I dove into using Claude Code to whip up an iPhone app for tracking 3D printer filament, I quickly learned that treating AI like a magic code genie with...
If you’re running a small business or managing IT for one, the latest zero-day flaw in Windows’ RasMan service—that critical background beast handling VPNs a...
OpenAI is cracking down on chatbot-infused toys like those from Alilo, which have been caught dishing out inappropriate chats on sex and risky topics to kids...
Google’s just dropped an emergency patch for the eighth Chrome zero-day vulnerability exploited in the wild this year, a sneaky buffer overflow in their LibA...
AI chatbots, meant to be helpful allies, are fumbling badly when users in crisis ask for suicide hotline numbers, often dishing out irrelevant resources, dod...
Big Tech is teaming up with the Linux Foundation to bring some much-needed order to the chaotic world of AI agents through the Autonomous Agents Interoperabi...
Microsoft’s AI-powered Copilot assistant is currently down for users in Europe and the UK, thanks to a nasty capacity scaling glitch triggered by a sudden tr...
In a no-holds-barred smackdown, Google’s Gemini handily outshone Microsoft’s Copilot across seven real-world tasks I threw at them, making it a clear favorit...
Barts Health NHS Trust, a big UK hospital operator, just fessed up to a data breach where the Clop ransomware gang exploited a nasty zero-day flaw in Oracle’...
I recently ran into a classic headache transcribing an interview audio from iPhone Notes—it nailed the words but totally botched separating speakers, turning...
Look, if you’re running React or Next
Italian researchers from Icaro Lab have uncovered a cheeky way to sidestep AI chatbot safeguards—simply wrap your shady requests in poetry, and suddenly, bot...
AI browsers like Microsoft’s Edge with Copilot and Google’s Chrome with Gemini are flipping the script on web surfing, turning your browser into a smart side...
The University of Phoenix recently admitted to a data breach stemming from a Clop ransomware gang’s exploitation of a zero-day vulnerability in Oracle’s E-Bu...
Watch out, SMBs and MSPs: cybercriminals are pulling off a slick phishing scam using fake Calendly invites that masquerade as recruiters from big names like ...
In the quirky world of x86 architecture, adding two integers isn’t as straightforward as you’d expect—thanks to its finicky two-operand limit that forces ins...
A 44-year-old Aussie hacker just got slapped with a seven-year-plus prison sentence for pulling off sneaky “evil twin” WiFi attacks, where he used a WiFi Pin...
Digging into this vintage beast, the Tektronix 4051—a 1975 vector graphics workstation that packed a Motorola 6800 CPU and up to 32KB of RAM into a hefty 35k...
The French Football Federation (FFF) recently fessed up to a data breach where hackers snagged access to their admin software via a hijacked account, exposin...
Malicious large language models like WormGPT 4 and KawaiiGPT are basically handing out cybercrime starter kits, letting script kiddies crank out sophisticate...
OpenAI just fessed up to a sneaky data slip involving some ChatGPT API users, all thanks to a smishing attack on their analytics vendor, Mixpanel—yeah, that ...
Mixpanel recently spilled the beans on a security hiccup involving a smishing attack that snuck up on a handful of customers back on November 8th, 2025, prov...
Meta’s cracking down on its WhatsApp platform by kicking out rival AI chatbots like OpenAI’s ChatGPT and Microsoft’s Copilot starting January 15, 2026, thank...
The FBI’s latest alert reveals that cybercriminals have swiped a whopping $262 million this year by impersonating bank support teams in sophisticated account...
Microsoft’s Exchange Online is throwing a curveball, blocking access to mailboxes via the classic Outlook desktop app for users in Asia Pacific and North Ame...
Harvard just fessed up to a sneaky voice phishing attack that infiltrated their Alumni Affairs and Development systems, exposing email addresses, phone numbe...
Look, if you’re still banking on that old-school fortress approach to cybersecurity—piling up firewalls like they’re medieval castle walls—you’re setting you...
Amazon’s latest AI wizardry, dubbed Autonomous Threat Analysis (ATA), is a smart move to outpace hackers in the escalating arms race of software security, es...
Cox Enterprises just fessed up to a nasty data breach where hackers exploited a zero-day vulnerability in Oracle’s E-Business Suite, snagging personal info f...
CISA is sounding the alarm on CVE-2025-61757, a sneaky pre-authentication remote code execution flaw in Oracle Identity Manager that’s already being exploite...
Look, if you’re running an SMB or MSP and still banking on those yawn-inducing anti-phishing training sessions that employees breeze through in under a minut...
Anthropic is flipping the script on its Claude chatbot, deciding to scoop up user chats and coding sessions as fodder for training its AI models starting Oct...
Anthropic has just dropped Claude Sonnet 4
ChatGPT is absolutely dominating the AI chatbot scene right now, pulling in massive user numbers and market share according to trackers like Comscore, Statco...
OpenAI’s latest updates to ChatGPT are geared toward turning it into a more reliable workhorse for teams, starting with a shared projects mode that lets coll...
At Subvertec, we’re all about cutting through the hype to help tech-savvy pros and small-business owners harness AI without getting burned—think of it as upg...
Subvertec’s take on this HN post? It’s a straightforward Python notebook that cuts through the fluff of linear algebra, using NumPy to walk you through every...
Neon, a sketchy app that lured users into recording their phone calls for quick cash to train AI models, has been yanked offline after a laughably simple sec...
Google’s 2025 DORA report reveals that AI is a double-edged sword for software dev teams, supercharging the efficient ones while exposing and exacerbating th...
Persian culture’s taarof ritual—think of it as a polite game of verbal ping-pong where refusing an offer three times is just a warm-up—totally stumps mainstr...
HubSpot’s engineering team kicked off their AI adventure with GitHub Copilot back in 2023, evolving from tentative trials to nearly everyone on board, thanks...
Discover how to cleverly prompt AI systems for maximum output without violating rules or ethical standards.
While clever prompting can help you avoid AI restrictions, understanding the ethical boundaries is critical.
Explore how hypothetical questions can help you get the information you need without triggering AI restrictions.
Learn how to provide context in your AI prompts to get more accurate and relevant responses while staying within guidelines.
Discover how rephrasing prompts can help you navigate AI restrictions without violating ethical guidelines.
Learn why AI systems have restrictions, and what types of content or actions they block to ensure ethical usage.
Learn how AI can help businesses comply with data privacy regulations like GDPR and CCPA, and safeguard customer data.
Discover how AI can personalize customer experiences, predict buying behavior, and create targeted marketing campaigns to boost customer loyalty and sales.
Learn how to implement small, manageable AI pilot projects that demonstrate immediate ROI and set the stage for future AI integration in your business.
Explore the typical costs associated with adopting AI, from pilot programs to full-scale deployments. Learn how to budget for your AI journey.
Explore how AI can streamline operations, enhance customer service, and optimize workflows to boost your business efficiency.
Discover the top 5 AI prompt techniques to ensure high-quality and efficient results from your AI tools. Learn how to optimize AI interactions for business s...
Learn how attackers exploit BitLocker and TPM with physical access during boot and discover strategies to mitigate these risks.
Learn how the RAMBO side-channel attack uses electromagnetic emissions to exfiltrate data from air-gapped systems without network access.
Enhance your Pi-hole with advanced configurations, custom block lists, performance tweaks, and integration with other security tools.
Learn how to set up Pi-hole using Docker Compose to block ads and secure your network across various hardware platforms.
Explore free alternative methods for backing up Windows data and protect your information effectively without relying on costly backup solutions.
Explore the 3-2-1 backup strategy, a reliable method for ensuring data redundancy and recovery. Learn how to protect your data from loss with this simple yet...
Understand the unique cybersecurity threats facing legal firms today. Discover how to safeguard your practice from data breaches, ransomware, and insider thr...
Learn why regular data backups are crucial for your business. Protect your valuable information from loss, corruption, and cyber threats by implementing a re...